Risk Definitions
Use Policies > Risk Definitions to view, define, edit, enable, or disable both managed and custom risk definitions.
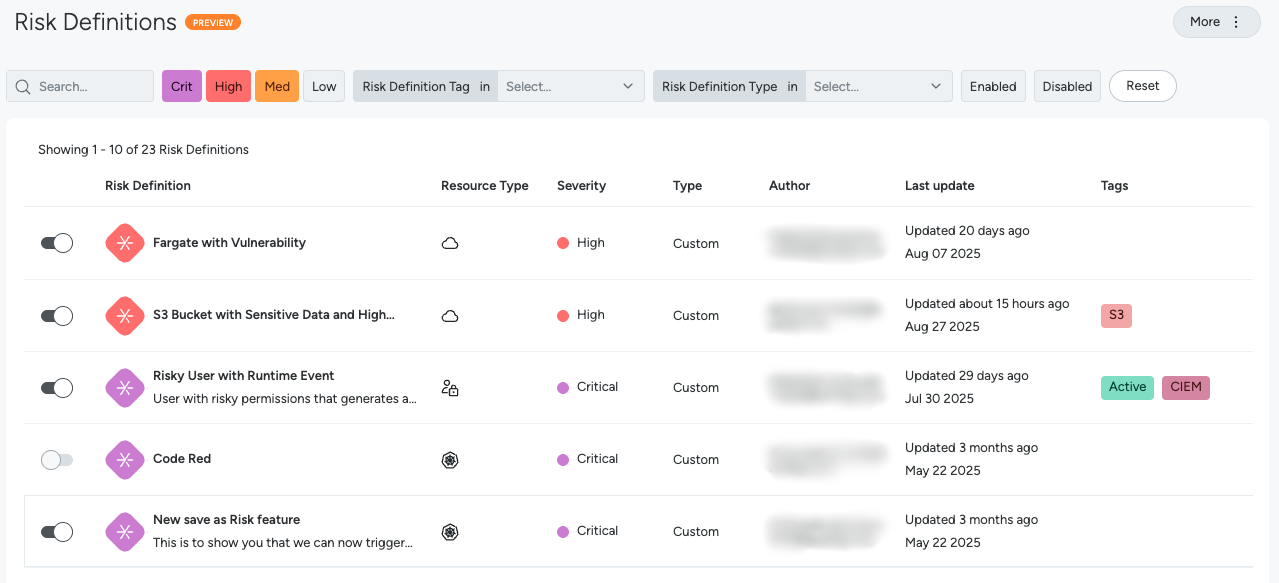
View and Manage Risk Definitions
The Risk Definitions page provides a consolidated view of all available risk definitions. You can filter by:
- Use the search bar to find Risk Definitions that contain the given search string.
- Use the Crit, High, Med and Low buttons to view Risk Definitions of critical, high, medium and low severities.
- Risk Definition Tag: Risk Definitions can be tagged with metadata indicating the nature of the risk, affected resource types, or anything else that may be relevant to your specific environment. For example
Exposed,Critical Vulnerability,HC Event,Kubernetes Workload,IAMRole, orService-BillingEngine. - Risk Definition Type: Managed (provided out of the box by Sysdig) or Custom (defined by the customer).
- Enabled Status: A Risk Definition that is enabled will continuously scan your environment for the conditions it’s designed to detect, generating risk findings when those conditions are met. When a Risk Definition is disabled, it is inactive and will not generate any new findings, allowing you to pause or remove a specific check without permanently deleting it.
The table includes the following columns:
- Risk Definition: The definition name and description.
- Resource Type: The type of the resource matched by the risk definition.
- Severity: The assigned severity level (Critical, High, Medium, Low).
- Type: Designates whether the definition is
Managed(authored by Sysdig) orCustom(created by the customer). - Author: The user who created the risk definition. Managed Risk Definitions will list
Sysdigas the author. - Last update: The timestamp of when the definition was last updated.
- Tags: The metadata tags assigned to the risk definition.
Select any Risk Definition row to display the SysQL query that defines it, as well as other metadata.
Create a New Custom Risk Definition
Sysdig provides a number of Managed Risk Definitions out-of-the-box. You can also create your own Custom Risk Definitions to tailor Risk Definitions to the needs of your organization’s cloud infrastructure. Custom Risk Definitons let you prioritize the risks and critical security issues that are the greatest threats to your circumstances. Additionally, the ability to customize using SysQL queries gives you greater control over your security posture, enhancing the efficiency and effectiveness of your security operations.
To create a Custom Risk Definition:
- Log in to Sysdig Secure.
- Select Policies > Risk Definitions.
- On the top-right corner of the page, select More > New Risk Definition.
The Create Query page appears.
- Define the query that will produce Risk Findings. See Build a Query.
Build a Query
On the Graph Search page, you can define a custom risk by using the SysQL query builder. For example, let’s build the following query:
EC2 with Critical Vulnerabilities
Click Start building your query and select Compute > EC2Instance.
Select That has Installed Package and click Go.
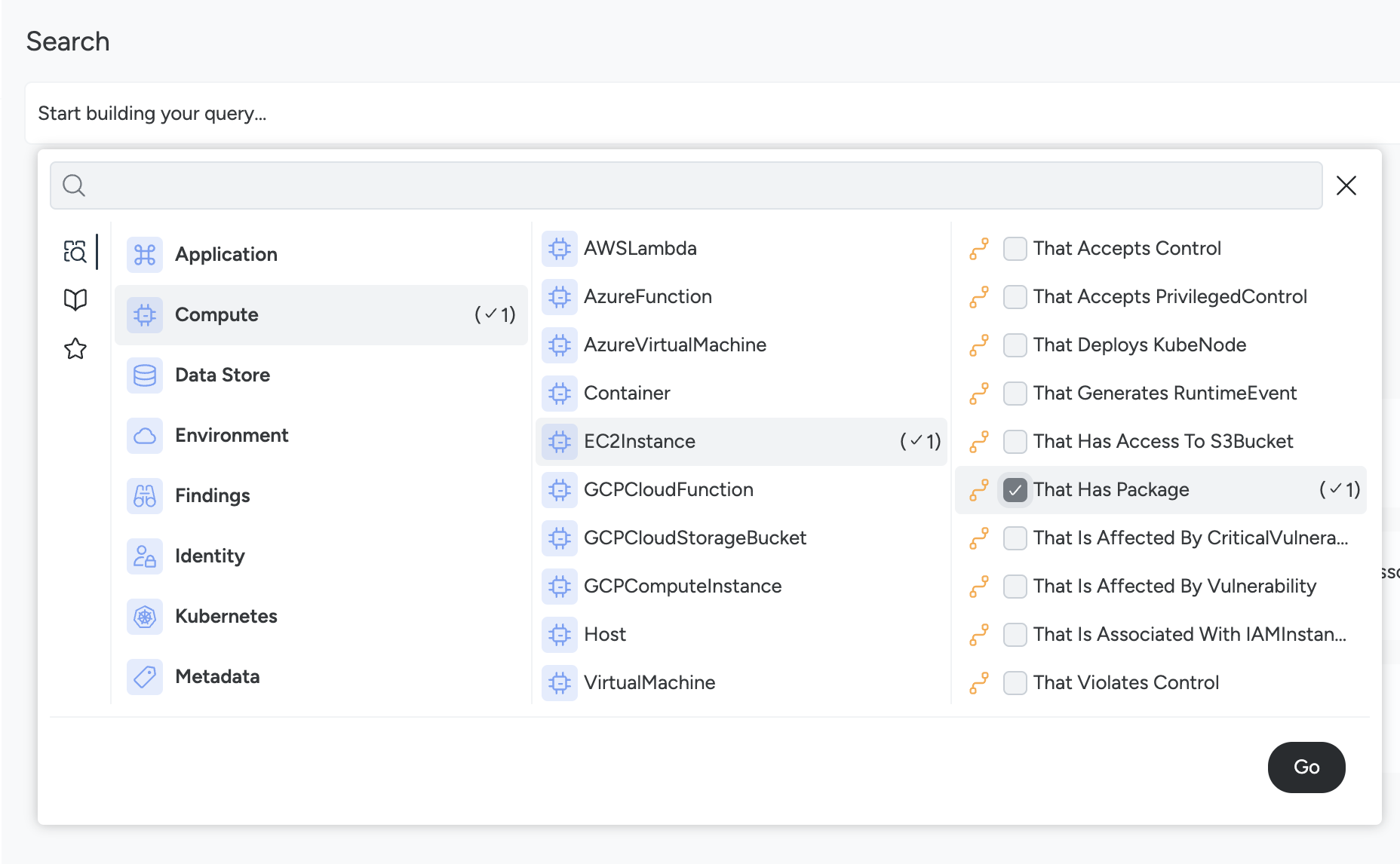
The query is ready to add more options.
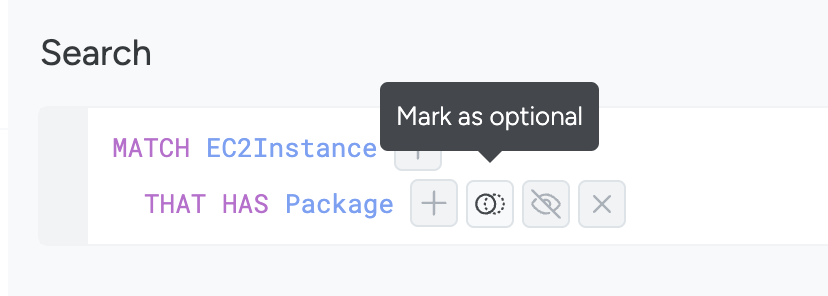
On the query builder, click the + icon next to
THAT HAS INSTALLED Package.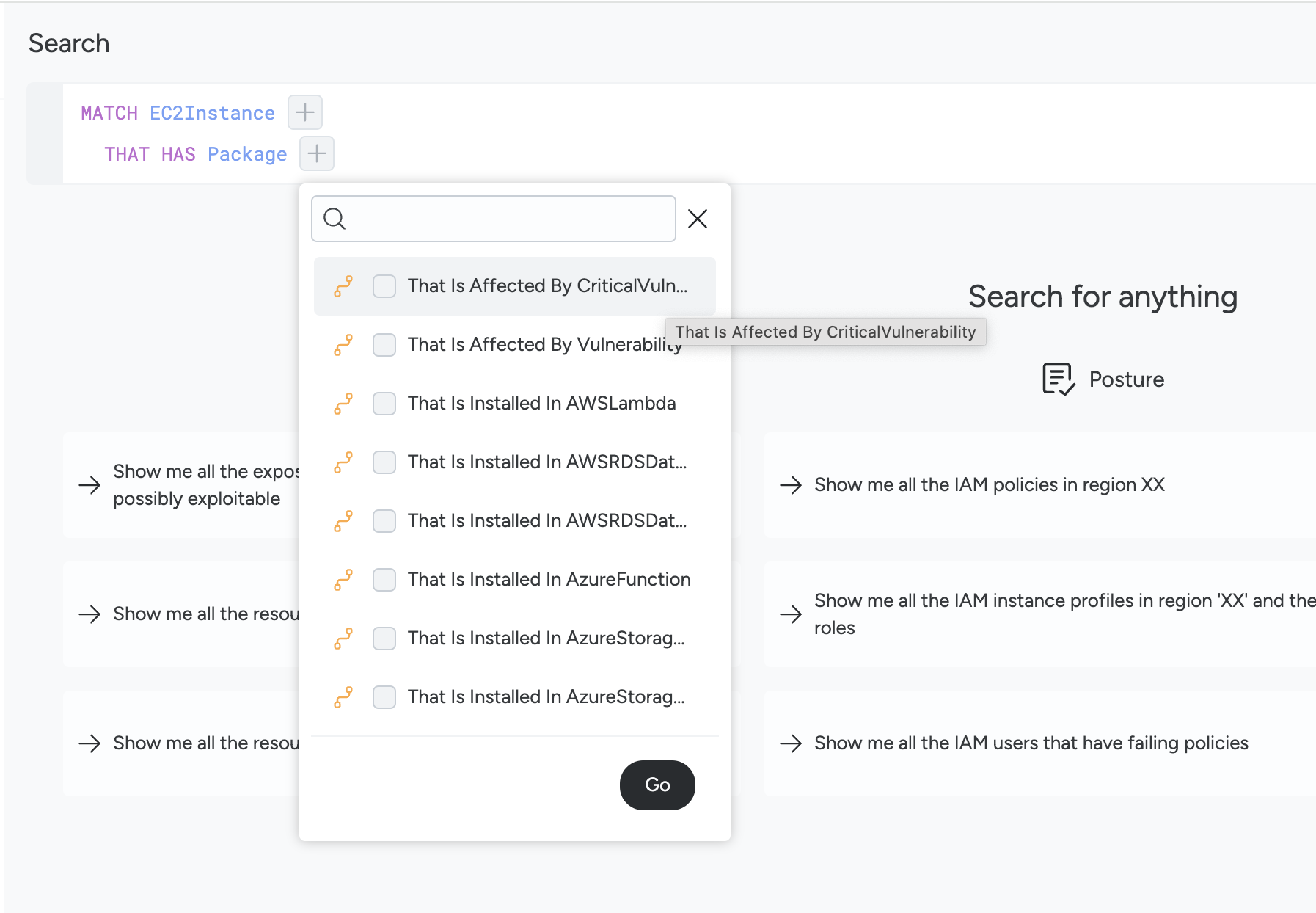
You have the option to hide, remove, or make the entity optional.
Select That Is Affected By Vulnerability.
Click the + icon to open the menu options and select Severity.
Click Go.
On the query builder, click the value for
severityand chooseCritical.Click Run to see all the entities that are at risk for this.
Click Save as Risk to save the custom risk that you have defined.
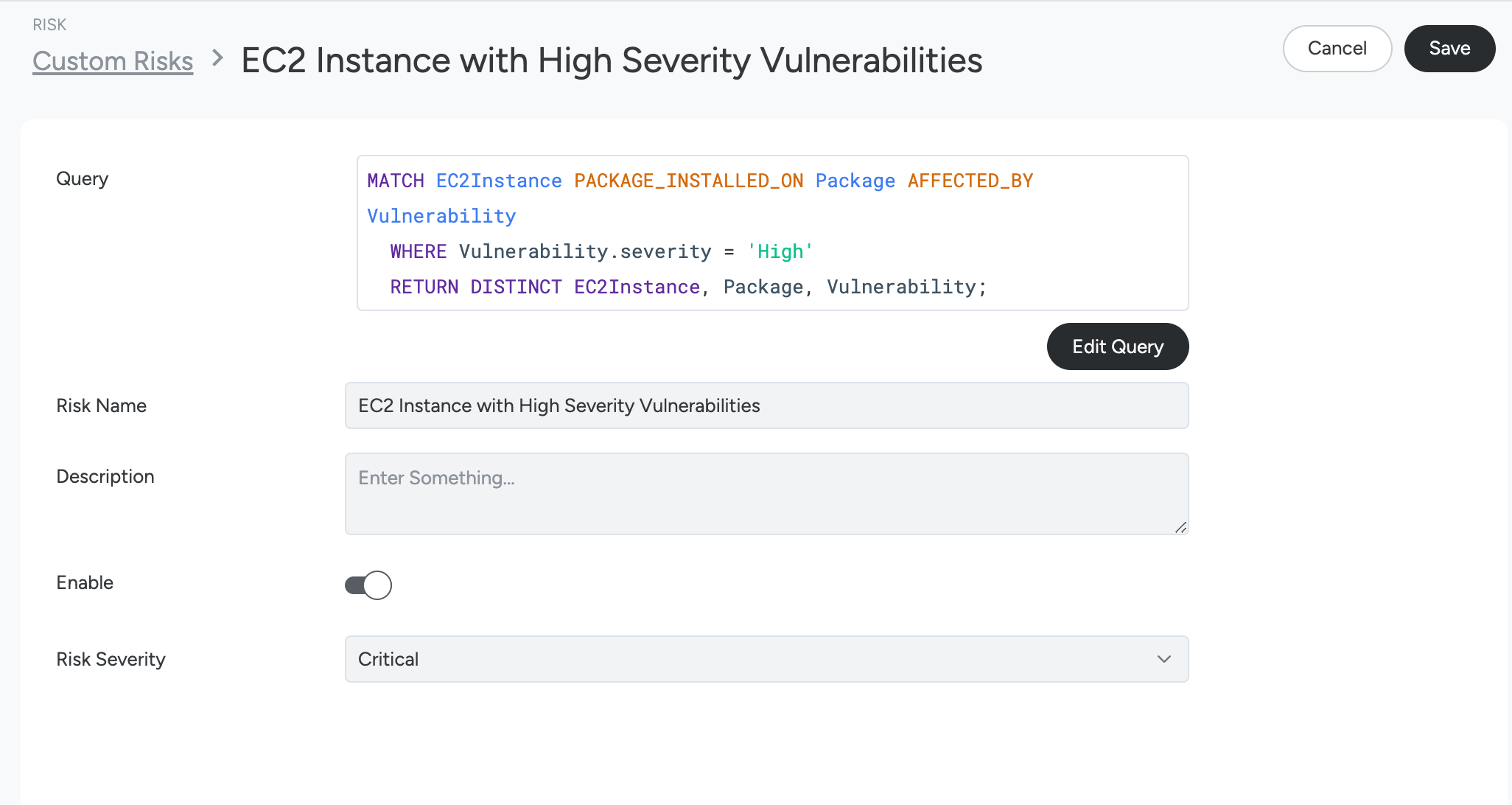
- Specify the following:
- Definition Name: A unique name to identify the custom risk that you have defined.
- Description: Details such as what this risk is.
- Risk Severity: Low, Medium, High, Critical.
- Optionally, enable the risk that you have just created.
- Optionally, specify any tags you may want to use when filtering or viewing the risk findings in your environment.
- Specify the following:
Click Save.
Once saved, you can view the risk you have just created on the Risk Definitions page.
Duplicate a Managed Risk Definition
You can use a Managed Risk Definition as a starting point for your Custom Risk Definition. This is desirable if an out of the box definition needs to be adjusted to suit your specific needs without having to build a new one from scratch. To do this:
- On the Policies > Risk Definitions page, select an available managed risk definition.
- Select the SysQL Query and copy the text.
- Click the Cancel button in the top right to return to the Risk Definitions page.
- On the top-right corner of the page, click More and then New Risk Definition.
- Click the icon with three vertical dots at the right of the query text box and select Paste. Your browser may ask you for permission to paste from the clipboard.
- Edit the query to adapt it to your specific needs.
- Continue from step 9 in the build a query section above.
Filter Risk Definitions
On the Policies > Risk Definitions page, you can search for and filter definitions you have created or that are managed by Sysdig in the following ways:
- Search Bar: Use the search bar to locate a risk by its name.
- Severity: Filter by using the severity of the risk.
- Status: Filter for definitions that are
EnabledorDisabled. - Risk Definition Type: Filter by Managed or Custom definitions.
- Risk Definition Tags: Filter by specific tags applied to the risk definitions.
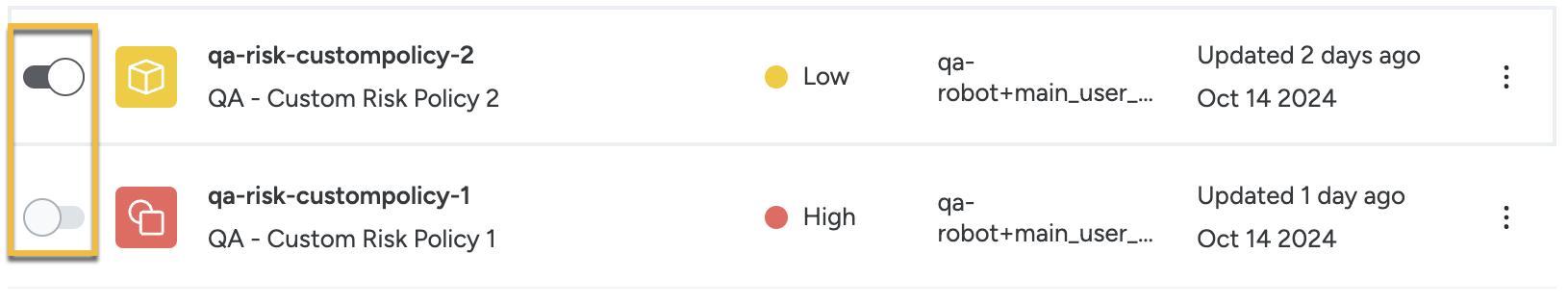
Activate or Deactivate a Risk Definition
On the Risk Definitions page, use the slider next to each definition to enable or disable it. You can disable both managed and custom definitions.
Edit a Custom Risk Definition
- On the Policies > Risk Definitions page, click the name of a custom risk definition.
- The definition’s details page appears. Click Edit Query to modify the SysQL, and click Update Query to save your changes.
- On the definition’s details page, you can change the name, description, severity, and tags.
- Make any desired changes and click Save.
Query Limitations
Consider the following constraints while building a query to create a Custom Risk rule:
The query must point to one of the following resources:
AWSLambdaAWSRDSDatabaseClusterAWSRDSDatabaseInstanceAzureFunctionAzureStorageAccountBlobServiceAzureStorageAccountBlobServiceContainerAzureVirtualMachineCloudOrKubeResourceEC2InstanceGCPCloudFunctionGCPCloudStorageBucketGCPComputeInstanceKubeWorkloadCloudResourceCloudUserCloudRoleCloudGroupCloudServiceIdentityCloudPolicyKubernetes ResourceS3BucketVirtualMachine
The query must have at least one filter applied to be evaluated as Risk. A filter can be:
- A
WHEREclause that filters out the resource - A relation matching some entity attached to the central resource This ensures that the result of the risk is not a plain list of resources but that these are filtered following some logic.
- A
The query must use only outgoing relations from entities that are resources:
The following query can’t be a risk, because it uses the Vulnerability as a “bridge” to get the workloads:
MATCH EC2Instance AFFECTED_BY Vulnerability THAT_AFFECTS KubeWorkloadThis ensures that the risk represents a possible attack surface and that does not represent connections between resources that are not logically connected.
A query can have only Resources as root nodes in the query.
A query requires at least one filter or relationship in the query.
Outgoing connections from the
Packageare not allowed except forVulnerabilities.To prevent users from creating invalid queries, outgoing connections are blocked from the following entities:
- Metadata
- Label
- Zone
- Region
- Policy
- Policy
- Vuln
- Vulnerability
- CriticalVulnerability
- Controls
- Control
- PrivilegedControl
- S3AcceptsHTTP
- S3VersioningDisabled
- ContainsAIPackage
- IAM Findings
- RiskFinding
- CompromisedState
- Runtime Events
- RuntimeEvent
- Metadata