Optimize GCP Group Entitlements
Review the permissions that you can grant to the Sysdig service account by enabling domain-wide delegation.
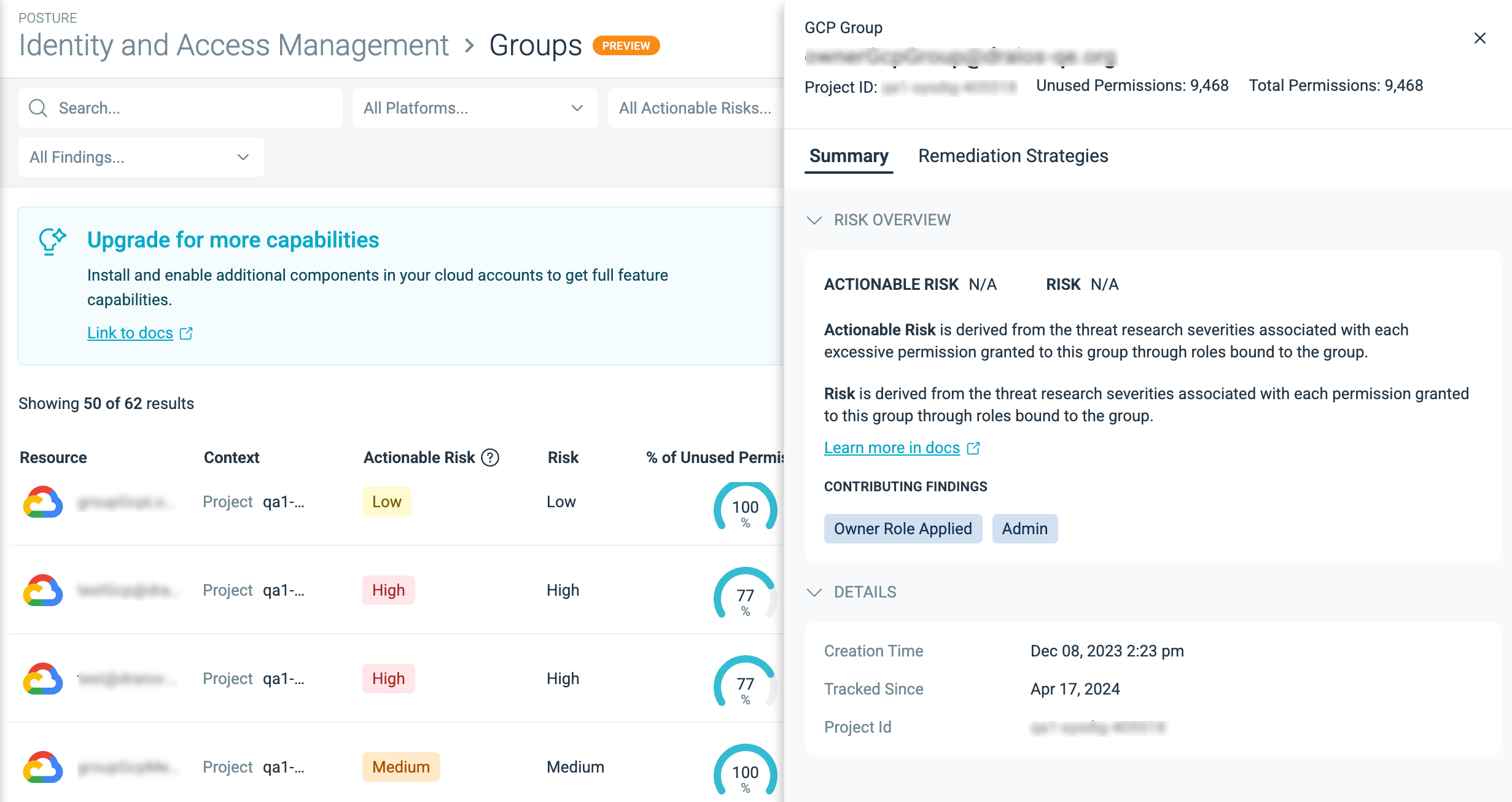
Manage Group Entitlements with Detail Drawers
To reduce the entitlements for a particular group, click on the account name to open the detail drawer and sub-tabs.
The Groups page organizes everything around the individual group.
- Summary: Displays the critical permissions issues detected for this group, sorted by Risk and Actionable Risk.
- Remediation Strategies: Summarizes all the potential strategies to reduce the permissions for this group
If Sysdig has been profiling a group for less than 90 days, you will see the following message:
We recommend a 90 day period to pass before applying remediation optimizations to establish a good baseline for used permissions.
Understand Group Permissions
Hover over the % Unused Permissions column to see the permissions granted to a GCP group:
- Total Permissions: The total number of permissions granted to a group from all the roles the group is bound to.
- Unused Permissions: The total number of unused permissions from all the roles that bound to a given group.
Apply Remediation Strategies
Click on the remediation recommendation to address the identity risk.
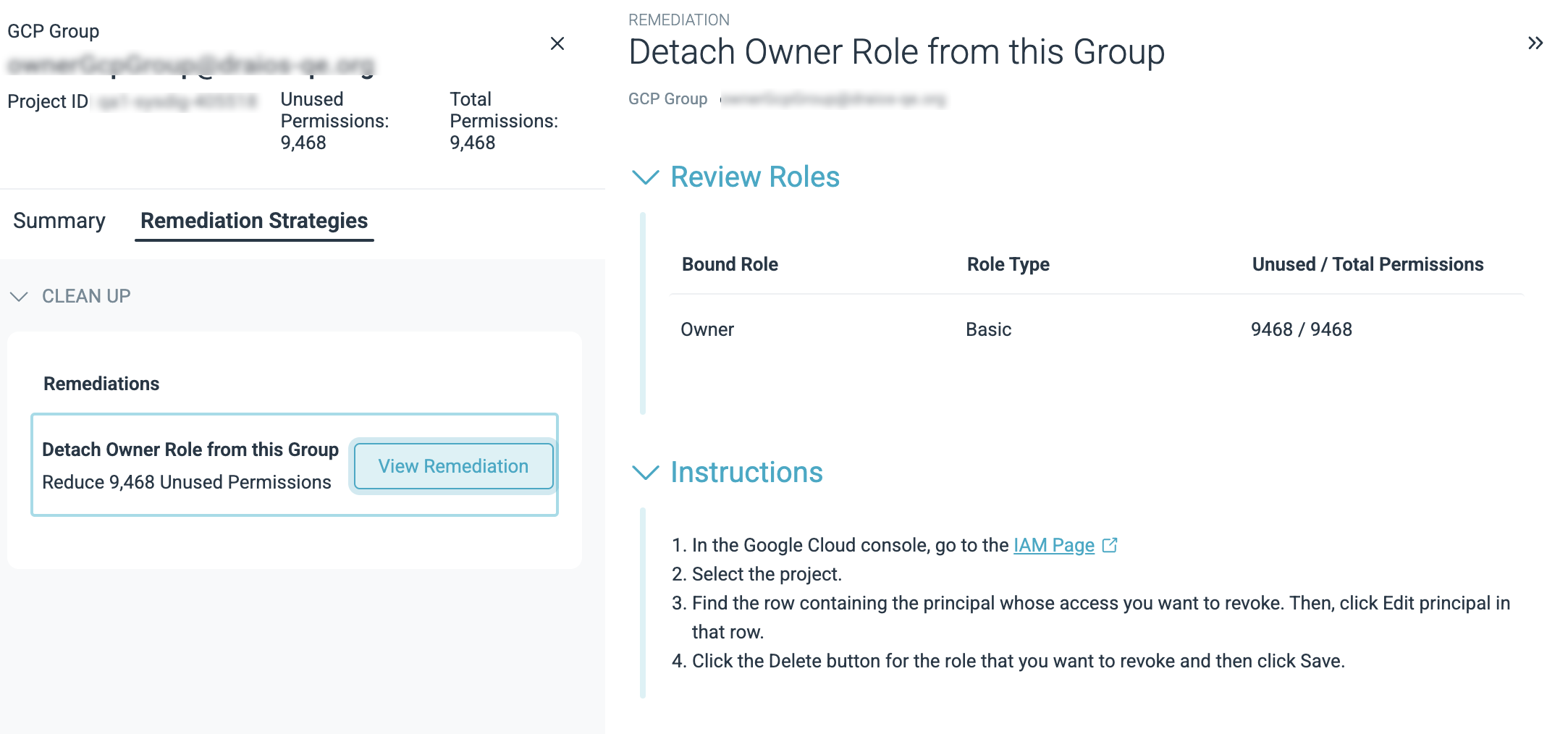
Detach Role from the Group
- All the roles that are totally unused by this group will get this recommendation
- If there are multiple detach recommendation, they are sorted based on the largest reduction in unused permissions.
Consolidate Permissions
Create a new custom role for the group with only a subset of used permissions.
This mechanism considers all the actions taken by this group across all its roles and consolidate them into one group-specific custom role. There will only be one custom role suggestion per group account.
Reduce Permissions with Existing Roles
Replace the existing role with a different role.
Sysdig recommends replacing a bound role with an existing role that contains all the permissions used by the current role but has fewer total permissions overall.
Feedback
Was this page helpful?
Glad to hear it! Please tell us how we can improve.
Sorry to hear that. Please tell us how we can improve.