Groups
Sysdig recommends creating Groups of user accounts and assigning permissions at the Group level rather than the individual User account level to facilitate administration tasks.
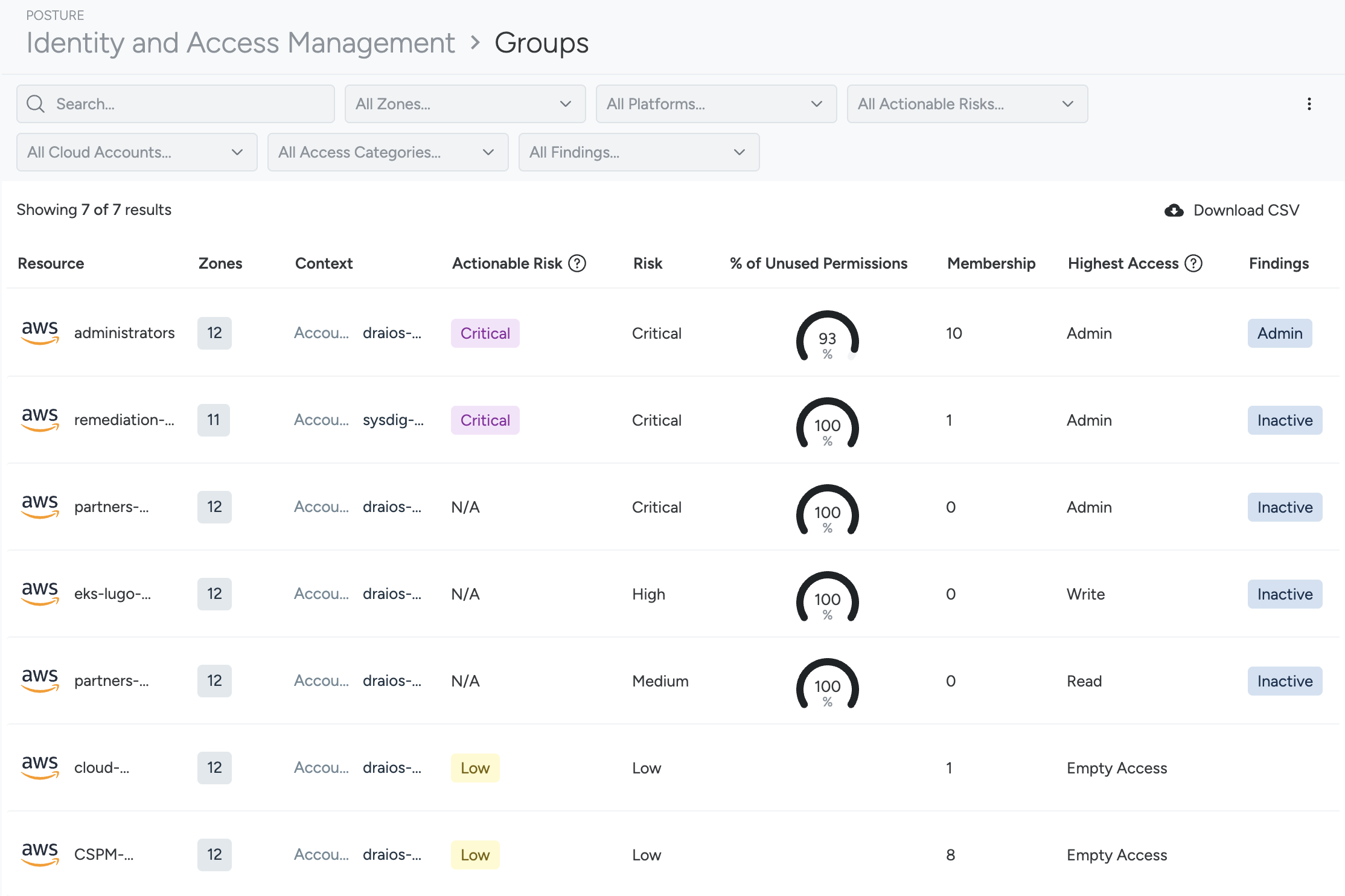
Filter and Sort Groups
Use the sortable columns to organize and filter Groups for assessing identity risks. You can sort groups based on the following criteria:
Actionable Risk
Actionable Risk focuses on unused permissions, while Risk looks at all permissions. Actionable Risk is designed to help you achieve Least Permissive access.
Values: Critical, High, Medium, Low
Risk
This is a calculation of risk based on all permissions. See Understanding Risk Scoring for more information.
Values: Critical, High, Medium, Low
% of Unused Permissions
This shows the number of unused permissions per total permissions for the group, shown as a percentage graph.
When remediating, immediately target the groups with the greatest exposure and refine them according to the suggestions.
Membership
The number of users who are part of this group.
Highest Access
Values:
- Admin: Admin access granted
- Write: Write access granted
- Read: Read access granted
- Empty Access: No permissions are granted at all
See Understand Highest Access.
Findings
A finding in Cloud Infrastructure Entitlement Management (CIEM) indicates poor security hygiene, either due to misconfiguration or inadequate identity security practices. The findings on Groups page include:
AdminInactive
Available Filters
- Search: Free text search on terms in the resource name
- Platform: by provider. For example, AWS
- Actionable Risks: By severity
- Cloud Accounts: Account name/number by cloud provider. For example, GCP
- Access Categories:
Admin,Write,Read, orEmpty Access - Findings:
Admin,Inactive
Next Steps
Feedback
Was this page helpful?
Glad to hear it! Please tell us how we can improve.
Sorry to hear that. Please tell us how we can improve.