Profiling
Profiling enables you to:
- Create Machine Learning policies, such as the Workload ML policy.
- View prioritized vulnerabilities in the In Use column of Vulnerability Runtime results, as described in Understand the In Use Column.
- Export prioritized runtime vulnerabilities from Sysdig to third-party vulnerability management software, as described in Risk Spotlight Integrations.
How Image Profiles Work
With image profiling enabled, the agents start sending “fingerprints” of what happened on the containers – network activity, files and directories accessed, processes run, and system calls used – and Sysdig Secure aggregates this information per image. Thus, for multiple containers based off the same image, running on different nodes, the profiler will collect and combine system activity into an image profile.
Internal algorithms determine these aspects of behavior:
- Length of time observed: Related to the image being in a learning/done learning state
- Consistency of behavior: Related to the confidence level of the observed behavior
Profile Contents
A container image profile is a collection of data points related to:
- Network activity
- TCP ports (in/out)
- UDP ports (in/out)
- Processes detected
- File system (informational only)
- Files (read/write)
- Directories (read/write)
- System calls detected
Disable or Enable Profiling
From Sysdig agent v.12.15+, the Profiling feature, the Helm chart parameters for the In Use and the Risk Spotlight Integration features are all automatically enabled.
You can disable or enable each of these manually, as described below.
When Profiling is enabled, the agent consumes more resources, both in memory and CPU. When the agent starts to use too many resources, it automatically and temporarily disables this feature, to avoid impacting its basic functionality.
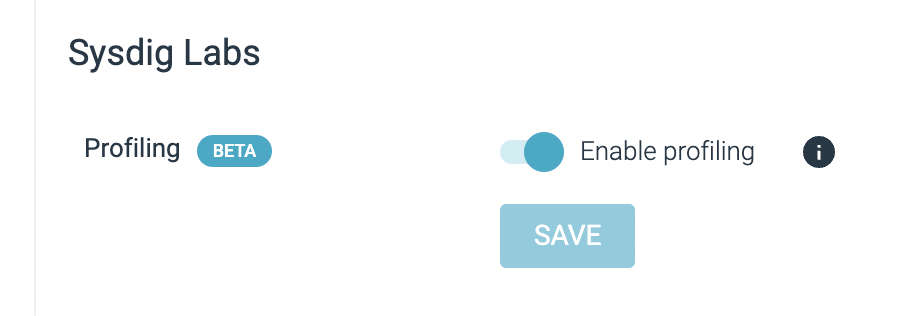
Log in to Sysdig Secure as Admin and navigate to Settings > User Profile.
Toggle the Profiling switch in the Sysdig Labs section.
Disable or Enable Helm Chart Parameters
If you disable Profiling, the best practice is to update your Helm charts to disable the In Use and Risk Spotlight Integration parameters.
Disable the In Use Parameter
The In Use column is displayed in the Vulnerabilities Runtime results in Sysdig Secure and requires an additional parameter for the Sysdig Agent.
See Risk Spotlight (In Use) for details.
To disable the In Use parameter, set the following in your sysdig-deploy Helm chart:
nodeAnalyzer.nodeAnalyzer.runtimeScanner.settings.eveEnabled=false
Disable the Risk Spotlight Parameters
Risk Spotlight integrations are used to enrich the vulnerability findings of external platforms with Sysdig’s runtime “in-use” insights. There are two integration models:
In-cluster: For Snyk
API-based: All others
See Risk Spotlight Integrations for details
Disable Risk Spotlight for Snyk
To disable Risk Spotlight for Snyk, set the following in your sysdig-deploy Helm chart:
-- set nodeAnalyzer.nodeAnalyzer.runtimeScanner.settings.eveEnabled=false
-- set nodeAnalyzer.nodeAnalyzer.runtimeScanner.eveConnector.deploy=false
Disable Risk Spotlight for Other Integrations
To disable Risk Spotlight for all other integrations, set the following in your sysdig-deploy Helm chart:
-- set nodeAnalyzer.nodeAnalyzer.runtimeScanner.settings.eveEnabled=false
Feedback
Was this page helpful?
Glad to hear it! Please tell us how we can improve.
Sorry to hear that. Please tell us how we can improve.